Protect your research participant data
The Ethnio platform is trusted by hundreds of organizations around the world. Our Service Level Agreement (SLA) outlines our commitment to protect and secure your data, and our Privacy Policy details how your participant’s data is used and stored safely.
Ethnio is proud to be certified by Prescient Security and Assurance as meeting the trust criteria for compliance with the AICPA Security Trust Principles and Criteria for Security (SOC2) Type 1 & Type 2. Ethnio’s service commitments and system requirements were achieved based on trust services relevant to Security, Availability, and Confidentiality set forth in TSP section 100. Additionally, Ethnio stores all Customer data in AWS US West (Oregon). Full independent service auditor’s reports for both Ethnio and AWS are available upon request.


GDPR
You decide what data you retain or delete. Easily set options to automatically delete screener responses, scheduling emails, and incentive records from all accounts – only store data for the time it is needed. Read more about Ethnio’s GDPR commitment.

Two factor authentication (2FA)
Keep your data secure by adding an extra level of protection to user accounts. Require all memeber enter an authentication token prior to gaining access to Ethnio. Read more about 2FA.
CCPA
Ethnio is fully compliant with the California Consumer Privacy Act (CCPA), a new California privacy law, where applicable. Many of our customers work hard on CCPA compliance, so it’s important that Ethnio supports that compliance by giving customers control of our platform and through our own terms and policies. Read more.

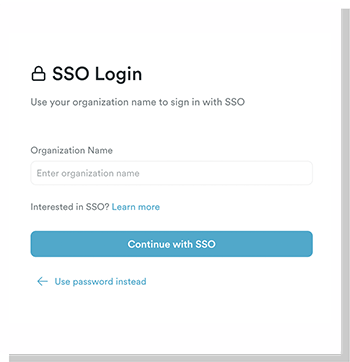
Single Sign-on (SSO)
Make signing in a breeze with SSO authentication. Get full access to Ethnio with one simple login. Ethnio supports most IdPs: from Okta, to OneLogin, and more. Read more about SSO.

Pentests & vulnerabilities
Ongoing penetration testing are performed, using the Cobalt platform, to ensure your data is safe and secure. This measures the security posture of a target system or environment and helps us scan for vulnerabilities through the year.
Physical security controls
AWS security includes a number of physical security features depending on the location, such as security guards, fencing, security feeds, intrusion detection technology, and other security measures.
Remote backups are performed regularly and stored in a different physical location from the main servers.

Full user access control
Define what users can see and do within your Ethnio account. Make sure data is safe from unauthorized users, even those within your organization – setting limits and permissions for billing, invoices, and incentives.


HIPAA
Ethnio fully supports HIPAA compliance, but no research tool or SaaS can ever be truly HIPAA compliant as it is not about the platform, but the users.
Ethnio’s security and privacy standards meet the highest tier for research software, including every component required for HIPAA compliance.
Security issues or questions?
If you have any questions or want to report a vulnerability, or if you suspect someone has violated Ethnio’s terms and conditions, please contact the Ethnio Security Team at security@ethn.io
